· Alex · security · 8 min read
Cloud Application Security
Challenges, best practices and Cloud Service Providers.

Cloud Application Security
In today’s increasingly digital world, we’re relying more and more on cloud computing to handle our data and applications. We can access our stuff from anywhere, at any time, and on any device. But there’s a catch - with all this convenience comes a responsibility to protect our applications and the data they manage. That’s where cloud application security comes into play. Application security is crucial to prevent unauthorized access, data breaches, and malicious attacks. In cloud computing, application security becomes even more vital. The cloud is a shared environment, and while cloud service providers do their part to keep the infrastructure secure, you have a responsibility to ensure your applications are up to snuff. This is often referred to as the shared responsibility model and it means that securing your applications in the cloud is not only important, but it’s also your duty. That’s why I’ve put together this blog post to walk you through the ins and outs of cloud application security.
What is Cloud Application Security?
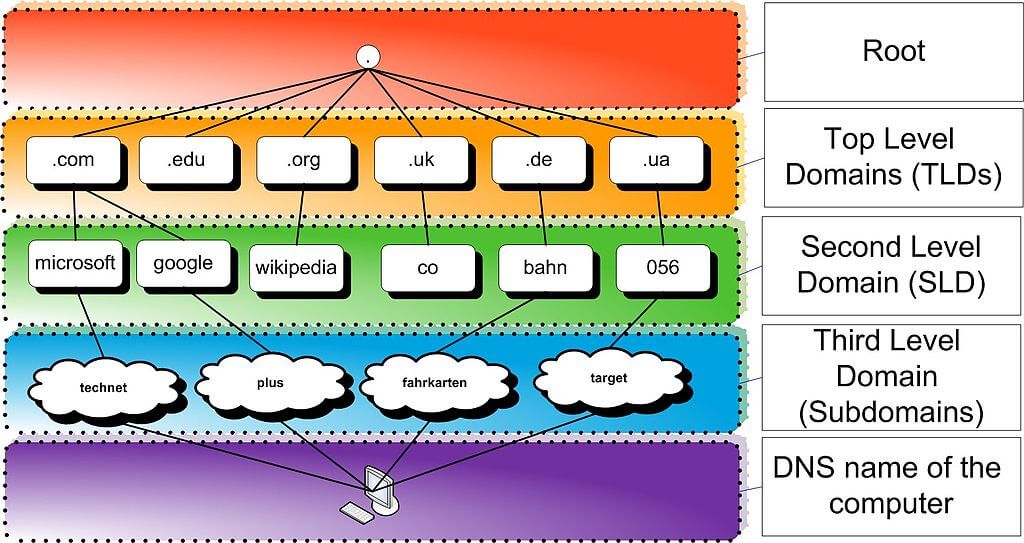
Cloud application security refers to the measures taken to protect your software applications from cyber threats. It’s all about keeping the bad guys out and making sure your application functions as it’s supposed to, without any nasty surprises. There are multiple layers of cloud security to consider when it comes to protecting your IT infrastructure. Here’s a quick rundown:
- Network security: This layer focuses on keeping your network safe from unauthorized access, hacking, and other attacks. Think firewalls, intrusion detection systems, VPNs, VPCs and network ACLs.
- Infrastructure security: This one’s all about securing the physical and virtual devices that make up your infrastructure, like servers, storage, and virtual machines.
- Endpoint security: This layer deals with securing individual devices like laptops, smartphones, and tablets that connect to your network.
Cloud Application Security is all about protecting the actual software applications themselves. This is super important because, at the end of the day, it’s your applications that are processing and storing sensitive data, and you want to make sure that data stays safe.
Cloud Application Security Challenges
So, you’ve decided to take your apps to the cloud. But hold up, we’ve got some important stuff to cover: cloud computing security challenges. As we mentioned earlier, when it comes to the cloud, there’s this thing called the “shared responsibility model.” Let’s break that down a bit. The shared responsibility model means that both you and your cloud service provider have a role to play in keeping your applications and data secure. Your provider is responsible for securing the underlying infrastructure, like the physical data centers, servers, and networking equipment. But as for your applications and data? That’s on you, buddy. Now, let’s chat about some unique security challenges that cloud-based applications face:
- Multi-tenancy: In the cloud, your apps often share resources with other users’ apps. While cloud providers have measures in place to isolate tenants, it’s still essential to ensure your app’s security is top-notch.
- Data storage and access: Storing sensitive data in the cloud can be convenient, but it’s crucial to ensure that only authorized users can access it. Proper encryption and access controls are a must.
- Increased attack surface: Moving your apps to the cloud can expose them to new threats, as they become accessible from anywhere on the internet. This makes it even more important to lock down your application security.
Now that we’ve touched on some challenges, let’s discuss the impact of insecure applications on businesses. Insecure applications can lead to data breaches, which can cost businesses big bucks in terms of fines, legal fees, and lost customers. Plus, there’s the damage to your brand reputation, which can be tough to bounce back from. And let’s not forget the potential loss of intellectual property and trade secrets, which could give your competitors an edge.
Best Practices for Cloud Application Security
Securing the application development lifecycle
- Secure coding practices: Start by making security a priority during the application development lifecycle. Train your developers in secure coding practices and make use of security frameworks and libraries to reduce the chances of introducing vulnerabilities.
- Regular code reviews and vulnerability scanning: Set up a process for regularly reviewing your code for potential security issues. Combine this with automated vulnerability scanning tools to catch any flaws before they become a problem.
Data encryption
- Encryption of data at rest: Make sure your data is encrypted when it’s stored on the file system. This can help protect sensitive information from unauthorized access or theft.
- Encryption of data in transit: Keep your data safe as it travels between your app and the user’s device by using secure communication protocols like HTTPS and TLS.
- Secret management: make sure to use a proper secrets manager (like AWS KMS), that allows for key rotation and secure key storage.
Identity and access management
- Implementing role-based access control: Restrict who can access your app and its data by assigning users specific roles and permissions. This helps ensure that only authorized individuals have access to sensitive information.
- Regularly reviewing and updating access privileges: Don’t set it and forget it! Regularly review and update user access privileges to make sure the right people have the right level of access.
Application security testing
- Static and dynamic application security testing: Use a mix of static and dynamic testing tools to analyze your app for security vulnerabilities. Static analysis checks your code without running it, while dynamic analysis tests your app while it’s running.
- Penetration testing: Get a professional ethical hacker to put your app through its paces, simulating real-world attacks to identify and fix any weaknesses.
API security
- Proper authentication and authorization: Make sure your APIs are secured with strong authentication and authorization mechanisms, like OAuth 2.0, to prevent unauthorized access.
- Rate limiting: Protect your APIs from abuse by implementing rate limiting.
Monitoring and logging
- Continuous monitoring for suspicious activities: Keep an eye on your app and its environment, watching for any signs of malicious activity. This can help you spot and address potential security issues before they become full-blown disasters.
- Regular log analysis and auditing: Make a habit of regularly reviewing and analyzing your app’s logs. This can help you identify patterns of suspicious behavior and provide valuable insights for future security improvements.
Infrastructure security
- Make sure to apply defense in depth and the principle of least privilege for your VPCs and infrastructure (security groups, network ACLs, firewalls, etc).
Leveraging Cloud Service Providers’ Security Features
Introduction to major cloud service providers’ security offerings
- Amazon Web Services (AWS): AWS provides a range of security features like AWS Shield for DDoS protection, AWS Identity and Access Management (IAM) for granular access control, and AWS Key Management Service (KMS) for encryption key management. Plus, they offer a bunch of monitoring tools like AWS CloudTrail and Amazon GuardDuty to help you keep an eye on your app’s security.
- Microsoft Azure: Azure has got your back with features like Azure Active Directory for identity and access management, Azure Security Center for unified security management, and Azure Private Link for secure access to your apps. They also offer Azure DDoS Protection and Azure Web Application Firewall to help fend off malicious attacks.
- Google Cloud Platform (GCP): GCP comes equipped with security offerings like Cloud Identity for access management, Google Cloud Armor for DDoS and application protection, and Cloud Key Management Service for managing your encryption keys. They also provide monitoring tools like Cloud Audit Logs and Cloud Security Command Center to help you stay on top of your app’s security.
Comparing and choosing the right security features for your application
Now that you’ve got a taste of what the major CSPs have to offer, it’s time to figure out which security features are right for your app. Here are some questions to consider:
- What kind of data does your app handle? If you’re dealing with sensitive information, strong encryption and access control features should be high on your list.
- Are you subject to any compliance requirements? Look for CSPs that offer features to help you meet regulations like GDPR, HIPAA, or PCI DSS.
- What’s your risk tolerance? If you’re in a high-risk industry or handling valuable data, you might want to invest in more advanced security features like DDoS protection, intrusion detection systems or WAFs (Web Application Firewalls).
Once you’ve got a handle on your app’s security needs, take some time to compare the offerings from different CSPs. You might find that one provider’s features align better with your requirements, or maybe a combination of features from multiple providers is the best fit.
Conclusion
We’ve covered a lot of ground, so let’s wrap things up with a quick recap and some words of encouragement. Remember, cloud application security is all about keeping your software applications safe from cyber threats in the cloud. Now that you’re armed with a bunch of best practices and a good understanding of the security features offered by major cloud service providers, it’s time to put that knowledge into action! Don’t be shy about implementing these best practices and investing in security solutions that’ll help keep your cloud-based apps safe and sound.
About the Author:
Application Security Engineer and Red-Teamer. Over 15 years of experience in Application Security, Software Engineering and Offensive Security. OSCE3 & OSCP Certified. CTF nerd.